Articles » What is and does DLL, BIN and DMG files?
What is and does DLL, BIN and DMG files?

Some of the most important files on computers today are DLL files, BIN files and DMG files. We have at Downloadcentral.dk made an explanation for each of the file types that explain what they really do. At the same time, we focus on what might be wrong with the use of these files. Eg. DLL files can slow down your computer and make it down if the same DLL file is used by several different pieces of software. Make sure your computer is working optimally with this program that offers a free system scan.
DLL files: Run your programs.
DLL files are dynamic link library files (also known as "dynamic link library" files) and are an integral part of Microsoft Windows and the software running on windows.
DLL files are shared between a variety of applications. Each DLL is a small bite of software code that contains instructions and tools for running a particular hardware device. In broader sense, Microsoft Dynamic Link Library files also have the extension. Ocx (this when files contain ActiveX objects), or.DRV for older system drivers.
The most common issues you will encounter with DLL files are when they are simply not present. Eg. When you add a new piece of hardware to your PC and you receive an error saying something like this: "DLL file WXYZ.DLL is missing: Install it now".

This means that your computer can not find the driver associated with the new hardware because it was not preinstalled with your operating system and you have not subsequently installed it either from a CD that accompanies the product or by downloading it from manufacturers website.
Like all other computer codes, DLL files can also contain errors and thus create conflicts with other software. Running a.DLL file with errors may result in a slow computer or the computer straight down.

To avoid these errors, it is always important to have the latest DLL files, which also add additional functionality, for example, or accommodate updated ActiveX components. However, modern computers share software components and this creates threats, as well as opportunities, and this is for good reason called "DLL Hell".

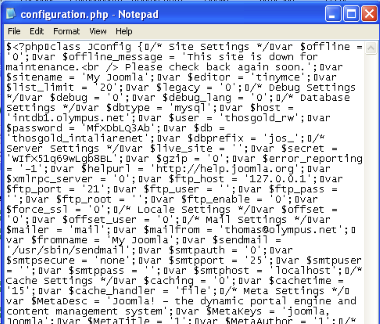
This could cause DLL problems due to incompatibility of a given DLL file used by different software. In other words, a query can use a version of a DLL file, while another program may overwrite this version with another (and older) version of the same DLL. Of course, it often creates problems for the earlier request. On top of that, "DLL Hell" may be caused by incorrect entries in the registry that point to the wrong DLL. As a final remark, it's unlikely that you should ever have to open or edit. DLL files (unless you are developer).
Also note that viruses hidden or masked as a DLL file can infect your PC, so be careful not to download them from the web or save them from emails unless you are sure it's clean.
BIN files: Software's indispensable workhorse.
The BIN extension type identifies binary files. These are listed on a variety of websites as being associated with a variety of programs including AVG (for update of the program), CDR Win CD (for image files), Micrografx Designer 7 and TenCORE. The Linux operating system also uses BIN files to identify executable files while.BIN files identify MacBinary II archive files on Apple computers.
As you probably already know, the binary numbering system is where numbers are represented as numbers (1) or zeroes (0). For example, the number 8 will be expressed as "1000" and the number 14 as "1110". These individual binary information (i.e., single or zero) are called bits, while binary files are generally considered as a series of 8 bit sequences called bytes.
So on a very rough plane, a binary file is actually a binary representation of a series of hexadecimal numbers between 0 and 256. Exactly what this series of numbers really means something that only the software designed to create or read these files can tell.
To this end, some binaries can be considered as "metadata" (literally "data about data" or you can think of it as "instructions on how different data is read") while other files have not included any metadata and are therefore called for flat binary files. The contents contained in these binaries can identify a variety of media, including images, audio content, formatted text, and compiled computer applications (also called binaries or objects).
The point here is that different applications will read the same hexadecimal numbers and see different things: maybe colors if read by an image viewer, notes of a music player or ASCII symbols of a word processor. If you try to open one. BIN file with a text editor, the order of "jumbled" characters will not display the underlying content of the text file, but instead show the characters the text editor thinks are the right ones to display.
The point of all this is that binaries are incredibly valuable workhorse for the technology industry but unless you have the right software they are almost completely unreadable.
DMG files: Images of Apple Mac software
To avoid doubts, we will begin to make it clear that.DMG files are not actual "images" of Apple Mac software.
The DMG file type identifies Macintosh OS X (ie, the latest version of Mac OS) disk image files. In connection with IT and computer software, the phrase "disk image" means something completely different from what we might otherwise believe. It may seem like a photograph of a disk, or an icon that illustrates a disc. In this context, "disk images" means copy of software and backups of the hard drive.
The traditional copy of a CD, DVD, hard disk or other media would require the computer to read the file structure in the media and copy it all to another place. However, this only works if the PC has access to all of these files and your PC will not (or at least not easily) be allowed to copy files that are protected and encrypted or otherwise not intended to become read by the system (such as the contents of boot disks). Disk imaging software takes a different approach to copying, making duplicates of the information actually on CDs, DVDs and other media - directly.

When copying the individual bits from the source media, disk imaging software can create an exact copy of the original content. There are a number of uses of these exact copies. Initially, the technology was used to simply backup the hard drive, or create a clone of a floppy disk, CD or DVD. But today it is a popular method of creating complete system backups that allow the system administrator to recover a damaged computer using the prints of a previous configuration of the given PC.
Similarly, the technology can be used in modern businesses where there are a large number of identical configured PCs. Here, system administrators do not want to install the same software on every single computer every time. Instead, install it correctly on one computer and then clone that computer's content (ie create a hard disk image) and copy it to each new PC where they need this configuration (also called ghosting).
The actual DMG files are specifically Apple's bid on a disk imaging technology, and the files are only recognized by Apple computers and Apple software. Apple uses DMG files to distribute software over the Internet as they offer additional useful features like password protection and data compression. When opened, Apple file manager (called Finder) will display the file as an additional hard drive on the system. Make sure your PC is running optimally with SpeedUpMyPC, which gives you a free system scan.
al! important; margin: auto! important; outline: initial! important; padding: initial! important; position: absolute; table layout: initial! important; text-align: initial! important; text-shadow: initial! important; width: initial! important; word-break: initial! important; word spacing: initial! important; overflow-wrap: initial! important; box-sizing: initial! important; display: initial! important; color: inherit! important; font size: 13px! important; font-family: X-LocaleSpecific, sans-serif, Tahoma, Helvetica! important; line-height: 13px! important; vertical-align: top! important; white-space: inherit! important; left: 147px; top: 1479px; opacity: 0.5; ">